Case Study
Security teams responsible for distributed networks face thousands of daily alerts from firewall logs, intrusion detection systems, and endpoint security platforms. Despite drowning in data, critical questions remain unanswered: Which devices are actually behind suspicious IP addresses? Is unusual activity an isolated incident or part of coordinated operations? How can you track threats when attackers rotate through proxies and VPNs?
The Challenge:
Traditional security tools exist in isolation—firewall logs show IP addresses, intrusion detection catches known patterns, endpoint security monitors individual devices. But these systems cannot reveal actual device movement, geographic patterns, or behavioral connections between seemingly unrelated events. Security decisions are based on incomplete intelligence, and significant threats hide in the gaps between monitoring tools.
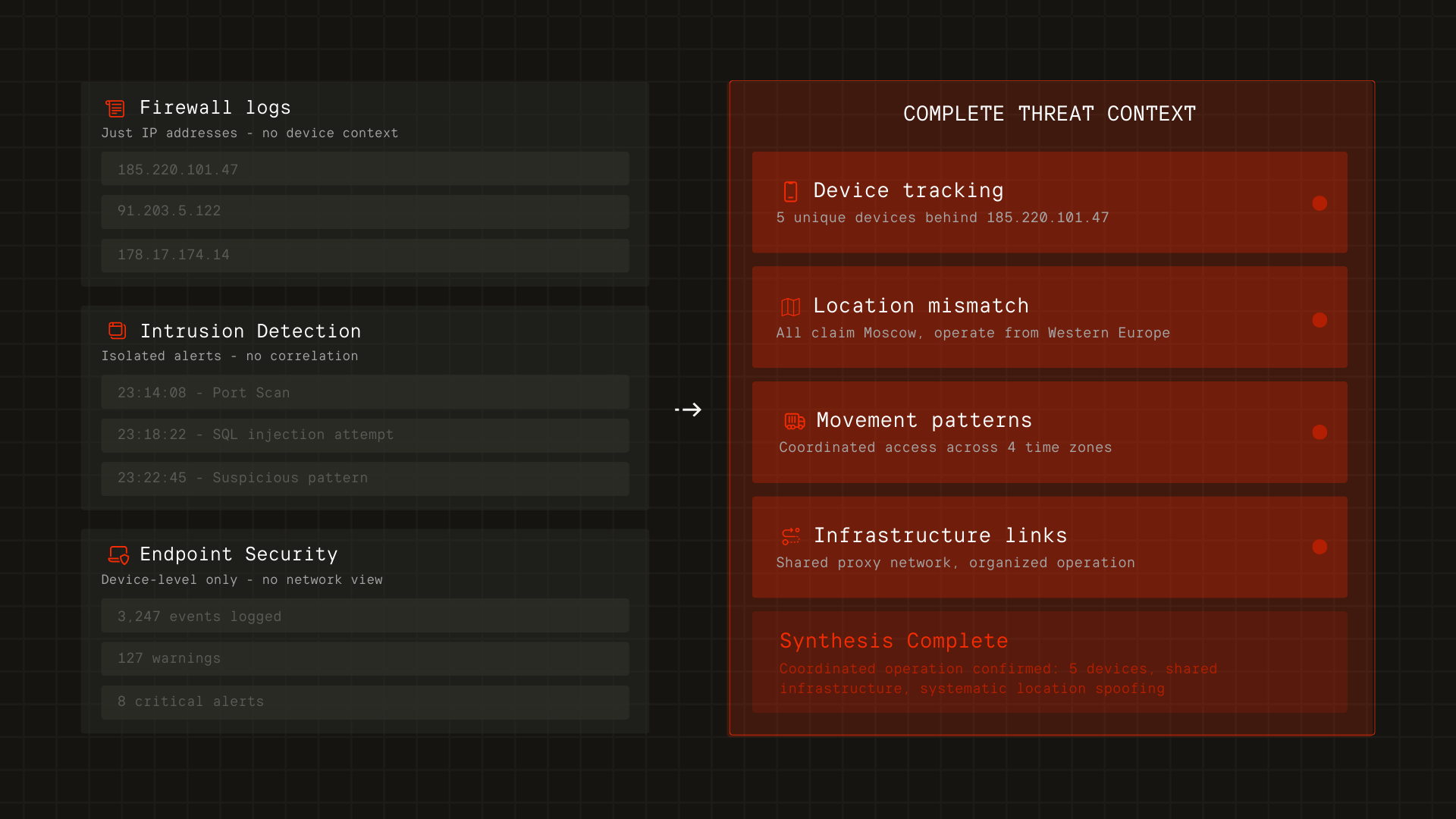
The Outcome:
By converging network intelligence with behavioral reality, security teams gain four critical capabilities invisible to traditional tools. Infrastructure mapping identifies devices connecting through suspicious IPs, revealing connections and compromise scope. Proxy network detection distinguishes legitimate privacy tools from malicious infrastructure. Behavioral validation correlates claimed locations with actual device movement, catching credential theft that bypasses traditional authentication. Network relationship analysis maps connections between devices sharing infrastructure, revealing coordinated operations invisible when tools monitor in isolation. This convergence layer transforms fragmented alerts into complete threat context—shifting security posture from reactive alert management to proactive defense based on what's actually happening.